Stop Treating IT Like a Cost Center. Start Using It as a Business Asset.
Many businesses are still evaluating technology through a model that made sense years ago, when IT was primarily about fixing problems, maintaining...
The shutdown has caused panic in many southeastern states.
The real-world consequences of a successful cyberattack have been clearly highlighted this week with the closure of one of the nation's largest pipelines due to ransomware.
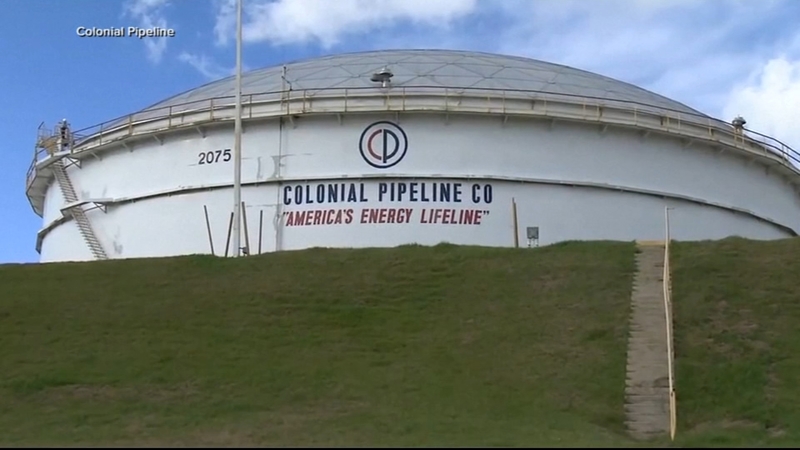
Colonial services seven airports and operates in 14 states. Its system is the biggest in the US, covering more than 5,500 miles and carrying more than 100 million gallons of fuel per day from Texas up the East Coast to New York. A tagline on its company's tanks, featured on its website, reads "America's Energy Lifeline."
On Friday, May 7th, in an effort to contain the breach, Colonial Pipeline system shut down 5,500 miles of pipeline on the East Coast, which it says carries 45% of the East Coast’s fuel supplies. Colonial Pipeline announced that they were the victim of a cyberattack, stating in their press release:
“We have since determined that this incident involves ransomware. In response, we proactively took certain systems offline to contain the threat, which has temporarily halted all pipeline operations, and affected some of our IT systems.”
On Monday, May 10th, the FBI identified hacker group “DarkSide”, a group that develops ransomware and sells it as a “ransomware as a service” business model. Meaning they develop and market ransomware hacking tools and sell them to other cybercriminals to carry out attacks.
There are few concrete details on how the cyberattack took place, and it is likely that this will not change until Colonial Pipeline and the third-party company brought in to investigate have concluded their analysis of the incident. It may have been an old, unpatched vulnerability in a system; a phishing email that successfully fooled an employee; the use of access credentials purchased or obtained on the Dark Web, or any other number of tactics employed by cybercriminals to infiltrate a company's network.
Bloomberg reported the company paid nearly $5 million in cryptocurrency to hackers within hours of the attack. This contradicts reports that the company had no intention of paying the ransomware.
According to Bloomberg, once they received the payment, the hackers provided a decrypting tool to restore its disabled computer network. The tool was so slow that the company continued using its own backups to help restore the system, one of the people familiar with the company’s efforts said.
A representative from Colonial declined to comment, as did a spokesperson for the National Security Council.
Given that the pipeline will take at least a few more days to come back into service, prices at the pump are rising dramatically as demand climbs and inventories of gasoline are reduced in states expected to be hit the hardest, including Georgia, North Carolina, South Carolina and Tennessee.
More than 17 percent of the stations in Georgia and Virginia were dry Wednesday, according to GasBuddy, and states as far as West Virginia and Kentucky also are running out. Major metropolitan areas have been hit hardest by the shortages, with more than 70 percent of the stations out of gasoline in Charlotte, Raleigh and Greenville, as well as roughly 60 percent of those in Norfolk and Atlanta, according to Patrick De Haan, GasBuddy’s head oil analyst.
@GasBuddyGuy Tweet, May 12th
Governors in Florida, North Carolina, Georgia, and Virginia have declared states of emergency and taken steps to relax fuel transport rules to ease some of the pain at the pump.
People are driving from station to station looking for gas. Gas stations have reported long lines of customers stocking up on fuel. They’re hoarding gas, filling up water bottles with extra gas, even taking the out-of-service bags off the pumps to see if they can squeeze out any bit of fuel.
North Carolina reported 7 out of 10 stations were out of fuel, even pausing all non-essential travel and asking employees to work from home to conserve fuel. A Virginia gas station had gas prices shown at $6.99 a gallon.
On May 12th, the US Consumer Product Safety Commission issued the following tweets:
@USCPSC Tweet, May 12th
Colonial Pipeline has brought parts of its fuel system back into operation, according to a statement posted on its website Tuesday evening, May 11th.
The Pipeline company said it delivered about 967,000 barrels, approximately 41 million gallons, to various markets, has taken delivery of an additional 2 million barrels from refineries in anticipation of a restart.
“Consistent with our safety policies and regulatory requirements, Colonial has increased aerial patrols of our pipeline right of way and deployed more than 50 personnel to walk and drive [about] 5,000 miles of pipeline each day,” the company said.
"Following this restart, it will take several days for the product delivery supply chain to return to normal," the company said in a statement. "Some markets served by Colonial Pipeline may experience, or continue to experience, intermittent service interruptions during the start-up period. Colonial will move as much gasoline, diesel, and jet fuel as is safely possible and will continue to do so until markets return to normal."
DarkSide is a relatively new group that follows the double extortion tactic, where hackers not only steal and encrypt the user’s data, they also threaten to make it public if the ransom demand is not paid. This technique effectively renders the security of backing up data as a precaution against a ransomware attack problematic.
DarkSide says it has a code of ethics and states the hackers will never attack hospitals, schools, universities, non-profit organizations, and government agencies.
Despite being a new group, it already has the reputation of making its operations more professional and organized. The group has a phone number and even a help desk to facilitate negotiations with victims, and they are making a great effort at collecting information about their victims. Not just technical information, but more general information about the company itself, like the organization’s size and estimated revenue.
By collecting information about the victims, the group is making sure the ransomware is only used against the “right targets.” The group claims they only target large, profitable companies in their ransomware attacks, and claim to have extorted millions of dollars from companies in an effort to "make the world a better place." The group even wrote in a forum that "some of the money the companies have paid will go to charity, although some charities have refused donations after realizing it was ransom money from ransomware attacks.
Hopefully, with the Pipeline reopened, we’ll start to see relief soon on the gas shortage.
Teknologize is a Managed Service Provider with clients throughout the Pacific Northwest with offices located in the Tri-Cities, Washington 509.396.6640, Yakima, Washington 509.396.6640, and Bend, Oregon 541.848.6072. Questions about cybersecurity? Give us a call today!

Many businesses are still evaluating technology through a model that made sense years ago, when IT was primarily about fixing problems, maintaining...
.png)
How a 100+ user professional services organization finished its Microsoft 365 migration — without deleting a single user account.
If your team uses Microsoft 365, there is a phishing attack making the rounds right now that most teams aren’t prepared to recognize yet. It does not...