8 min read
Microsoft 365 Direct Send Phishing: What We're Seeing and Why It Matters
If your team uses Microsoft 365, there is a phishing attack making the rounds right now that most teams aren’t prepared to recognize yet. It does not...
Articles for business leaders covering topics such as technology, cybersecurity, and compliance.

8 min read
If your team uses Microsoft 365, there is a phishing attack making the rounds right now that most teams aren’t prepared to recognize yet. It does not...

4 min read
February has a rhythm every business owner knows. Your accountant is asking for documents. Your bookkeeper is reconciling numbers. Payroll is...
%20Enabling%20Secure%20Growth%20for%20Small%20Businesses.png?width=1080&height=1080&name=Endpoint%20Detection%20and%20Response%20(EDR)%20Enabling%20Secure%20Growth%20for%20Small%20Businesses.png)
3 min read
Cybercriminals don’t go after businesses because they’re big. They go after businesses because they’re accessible. According to the IBM Cost of a...

3 min read
“When did this happen?” “About a year ago… well, thirteen months, actually.”

2 min read
Artificial intelligence is everywhere, helping small businesses automate workflows, streamline processes, and boost productivity. But here’s the flip...

5 min read
What are the most common compliance requirements small businesses miss, and how much can noncompliance really cost? Many small businesses overlook...

2 min read
Cybercriminals Aren’t Breaking In. They’re Logging In. For years, business owners pictured hackers as people “breaking in” through firewalls. Today,...

2 min read
October isn’t just the start of fall in the Pacific Northwest, it’s also Cybersecurity Awareness Month, a perfect reminder for business leaders to...

2 min read
If you’ve ever had that sinking feeling when your systems go down or your IT guy only shows up when something breaks, you’re not alone. Too many...
2 min read
Hackers are already using AI to scale phishing, mimic your leadership’s voice, and guess passwords with alarming accuracy. Believing the old myths...

3 min read
When choosing a business continuity and disaster recovery (BCDR) solution, many small and mid-sized businesses (SMBs) see quotes for Veeam that...

3 min read
If your team works from anywhere, uses a mix of personal and company devices, and is dabbling with ChatGPT, you need to keep reading.

3 min read
AI-driven chatbots like ChatGPT, Google Gemini, Microsoft Copilot, and DeepSeek are rapidly transforming the way small to medium-sized businesses...
.png?width=1200&height=900&name=Old%20Tech%20(1).png)
2 min read
When was the last time you tossed out an old computer, server, or smartphone from your office? Maybe it was collecting dust in the corner. Perhaps...

3 min read
If you run a construction company or any small business that deals with many vendors and invoices, you need to know that you’re on the radar of...
.png?width=1200&height=900&name=W11%20EOS%20Countdown%20(1).png)
2 min read
Still using Windows 10 in your business? It's time to face the facts: the clock is ticking. On October 14, 2025, Microsoft ends all support for...

2 min read
Are Your Employees Putting Your Business at Risk Without Realizing It? If you run a small or medium-sized business in Washington or Oregon, you're...
3 min read
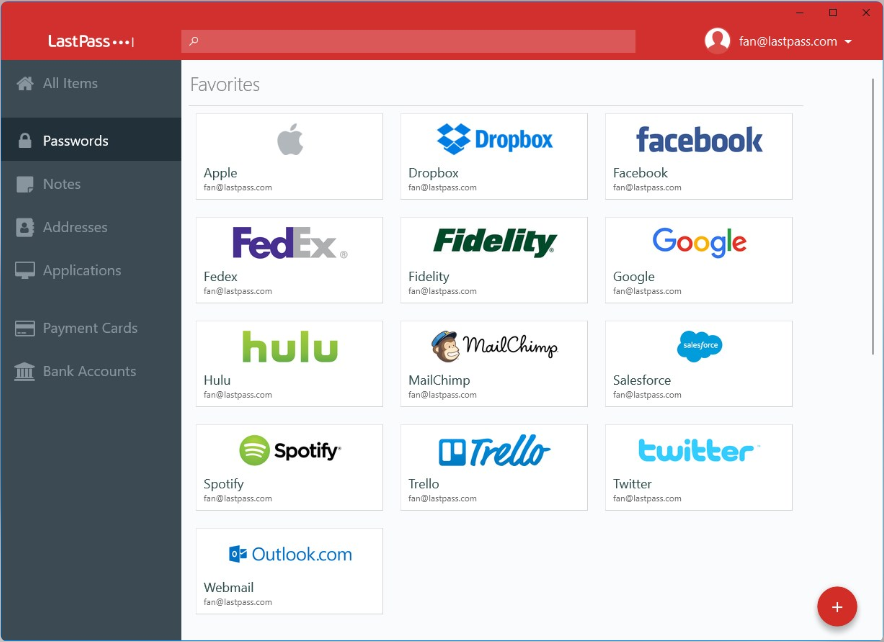
In today’s world, managing passwords can feel overwhelming, especially when every website demands longer, more complicated combinations of letters,...

3 min read
Protecting sensitive information is a year-round priority for small and mid-sized businesses (SMBs) in Washington and Oregon.

2 min read
When was the last time your network had a full health check? If you're like many businesses, the answer might be "never" or "longer ago than it...

4 min read
Yes. As a CPA, you manage sensitive client data every day, including personal financial details, social security numbers, tax information, and more....

2 min read
Recently, the FBI issued a fresh warning about "smishing" scams involving fake toll-road notifications sent via text messages. Scammers are targeting...
.png?width=1200&height=900&name=Bank%20Fraud%20(1).png)
2 min read
Imagine waking up, grabbing your morning coffee, and checking your business bank account, only to see thousands, or even hundreds of thousands, of...

2 min read
Tax season is already stressful enough—tight deadlines, demanding clients, and long hours. But cybercriminals are counting on that chaos to catch...

2 min read
Imagine this: You’re running your business. It’s a typical morning, you’re sipping coffee, checking emails, and planning your day. What you don’t...
.png?width=1200&height=900&name=Lock%20Computer%20(1200%20x%20900%20px).png)
2 min read
In today’s digital world, security isn’t just about strong passwords and firewalls - it starts with simple habits like locking your computer screen...

3 min read
Windows 10’s end-of-life is fast approaching. With official support ending in October 2025, businesses and individuals relying on the operating...
.png?width=1200&height=900&name=LOTL%20(1).png)
3 min read
As cyber threats continue to evolve, attackers are finding new ways to bypass even the most advanced security systems. One of the techniques gaining...
.png?width=1200&height=900&name=data%20strategy%20(1).png)
3 min read
Data is the backbone of any successful business, but many organizations unintentionally undervalue their data by treating it as a secondary priority...
3 min read
Our smartphones are our lifelines. They keep us connected, entertained, and organized. But our devices can easily become cluttered with so many apps...

3 min read
The holiday season is here, bringing the excitement of discovering amazing deals during Black Friday and Cyber Monday. But while you’re hunting for...
.png?width=1200&height=900&name=Proactive%20IT%20(2).png)
2 min read
Ah, the holiday season, when everything sparkles, sales soar, and your to-do list rivals Santa's naughty and nice list. For businesses, it's a time...

1 min read
Cybersecurity Awareness Month is a great reminder to update our devices and software regularly. When we delay software updates, we risk exposing our...

3 min read
October is Cybersecurity Awareness Month, a perfect time to raise awareness about phishing attacks and how to protect yourself from these deceptive...

2 min read
Artificial Intelligence (AI) is transforming the way we live, work, and interact online, offering incredible opportunities for efficiency and...

2 min read
October is Cybersecurity Awareness Month, making it the perfect time to boost your online security. One of the easiest and most effective ways to...