5 min read
Hybrid Identity Purgatory: A Hybrid-to-Cloud Microsoft 365 Migration Story (Without Data Loss)
How a 100+ user professional services organization finished its Microsoft 365 migration — without deleting a single user account.
Articles for business leaders covering topics such as technology, cybersecurity, and compliance.
.png?width=1080&height=1080&name=Hybrid%20Identity%20Purgatory%20A%20Hybrid-to-Cloud%20Microsoft%20365%20Migration%20Story%20(Without%20Data%20Loss).png)
5 min read
How a 100+ user professional services organization finished its Microsoft 365 migration — without deleting a single user account.

8 min read
If your team uses Microsoft 365, there is a phishing attack making the rounds right now that most teams aren’t prepared to recognize yet. It does not...

6 min read
It's Monday morning. You walk into the office with a plan. This is the week things move forward.

4 min read
Over the past year, artificial intelligence has moved from a niche technology topic to a central driver of global technology investment....

4 min read
February has a rhythm every business owner knows. Your accountant is asking for documents. Your bookkeeper is reconciling numbers. Payroll is...
%20Enabling%20Secure%20Growth%20for%20Small%20Businesses.png?width=1080&height=1080&name=Endpoint%20Detection%20and%20Response%20(EDR)%20Enabling%20Secure%20Growth%20for%20Small%20Businesses.png)
3 min read
Cybercriminals don’t go after businesses because they’re big. They go after businesses because they’re accessible. According to the IBM Cost of a...

3 min read
IT Support Companies Can All Sound the Same, Until You Know What to Look For Business owners all want the same thing from their IT: reliability,...

5 min read
Many SMBs don’t actually have an IT budget; they have a list of last year’s expenses. Everything goes into one bucket, and next year’s “budget” is...

3 min read
“When did this happen?” “About a year ago… well, thirteen months, actually.”

2 min read
Artificial intelligence is everywhere, helping small businesses automate workflows, streamline processes, and boost productivity. But here’s the flip...

3 min read
What happens to my business computers after Windows 10 support ends on October 14, 2025? If your company is still running Windows 10, the answer is...

2 min read
If you’ve ever had that sinking feeling when your systems go down or your IT guy only shows up when something breaks, you’re not alone. Too many...

2 min read
Microsoft has set an official deadline: October 14, 2025, marks the end of Windows 10 support. After this date, the operating system will no longer...

3 min read
When choosing a business continuity and disaster recovery (BCDR) solution, many small and mid-sized businesses (SMBs) see quotes for Veeam that...
.png?width=1080&height=1080&name=July%201%202025%20(1).png)
2 min read
If your nonprofit relies on Microsoft 365 Business Premium or Office 365 E1 through Microsoft’s grant program, there’s a critical change you need to...

3 min read
If you run a construction company or any small business that deals with many vendors and invoices, you need to know that you’re on the radar of...
.png?width=1200&height=900&name=W11%20EOS%20Countdown%20(1).png)
2 min read
Still using Windows 10 in your business? It's time to face the facts: the clock is ticking. On October 14, 2025, Microsoft ends all support for...

2 min read
Are Your Employees Putting Your Business at Risk Without Realizing It? If you run a small or medium-sized business in Washington or Oregon, you're...
3 min read
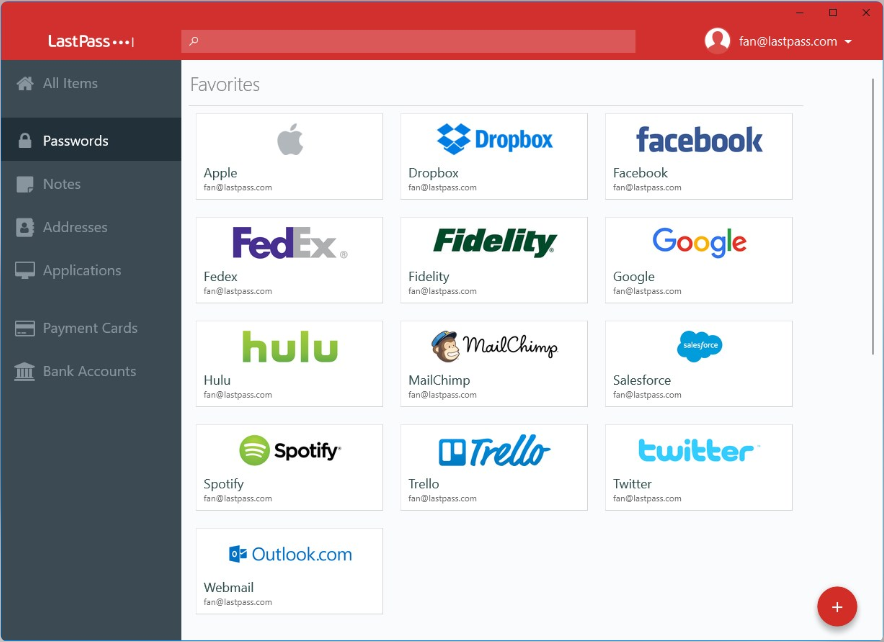
In today’s world, managing passwords can feel overwhelming, especially when every website demands longer, more complicated combinations of letters,...

3 min read
Every business owner knows the stress of managing technology—especially when it's not aligned with your business goals. Ever felt like your IT...

4 min read
Financials, market expansion, and strategic growth often drive Mergers & Acquisitions (M&A) and Divestitures. Due diligence focuses heavily on...

3 min read
Windows 10’s end-of-life is fast approaching. With official support ending in October 2025, businesses and individuals relying on the operating...
.png?width=1200&height=900&name=data%20strategy%20(1).png)
3 min read
Data is the backbone of any successful business, but many organizations unintentionally undervalue their data by treating it as a secondary priority...
.png?width=1200&height=900&name=Proactive%20IT%20(2).png)
2 min read
Ah, the holiday season, when everything sparkles, sales soar, and your to-do list rivals Santa's naughty and nice list. For businesses, it's a time...

2 min read
IMPORTANT: Microsoft recently announced the official end of support for Windows 10 on October 14, 2025. After this date, while your Windows 10 PCs...
4 min read
Have you ever mentioned a product or service near your phone and then suddenly seen ads for it on your social media feed? If you have, you’re not...

1 min read
Cybersecurity Awareness Month is a great reminder to update our devices and software regularly. When we delay software updates, we risk exposing our...

3 min read
October is Cybersecurity Awareness Month, a perfect time to raise awareness about phishing attacks and how to protect yourself from these deceptive...

2 min read
Artificial Intelligence (AI) is transforming the way we live, work, and interact online, offering incredible opportunities for efficiency and...

2 min read
October is Cybersecurity Awareness Month, making it the perfect time to boost your online security. One of the easiest and most effective ways to...

2 min read
Is your business losing money due to outdated technology? Chances are, the answer is yes. A recent survey by Deloitte found that 82% of companies...
.png?width=1200&height=900&name=W11%20(2).png)
3 min read
As October 14, 2025, approaches, businesses need to prepare for the end of support for Windows 10. Microsoft has announced that after this date, they...
.png?width=1200&height=900&name=WBA%20Issues%20%26%20Answers%20(6).png)
3 min read
A WBA Issues and Answers publication. Dan Morgan addresses regulated domains such as .bank and cybersecurity considerations around domain spoofing...
4 min read
Small and medium-sized businesses (SMBs) are the engines driving our economy. In today’s fast-paced, digitally dependent world, a robust IT...

2 min read
In today's fast-paced business world, reliable technology is crucial. Many companies, however, find themselves hindered by inadequate tech support....

3 min read
Technology can offer a strategic advantage for businesses across all industries when used effectively. However, business owners often face common...