2 min read
Raising Digital Citizens: Keeping Kids Safe Online During Cybersecurity Awareness Month
The Internet offers children a world of learning, entertainment, and social engagement. However, just like the real world, it comes with risks....
Articles for business leaders covering topics such as technology, cybersecurity, and compliance.

2 min read
The Internet offers children a world of learning, entertainment, and social engagement. However, just like the real world, it comes with risks....

2 min read
Weak passwords are one of the most common ways cybercriminals gain access to accounts. With Cybersecurity Awareness Month upon us, it’s the perfect...

3 min read
October isn’t just about cozy sweaters and pumpkin spice; it’s also Cybersecurity Awareness Month, a time dedicated to raising awareness about the...
2 min read
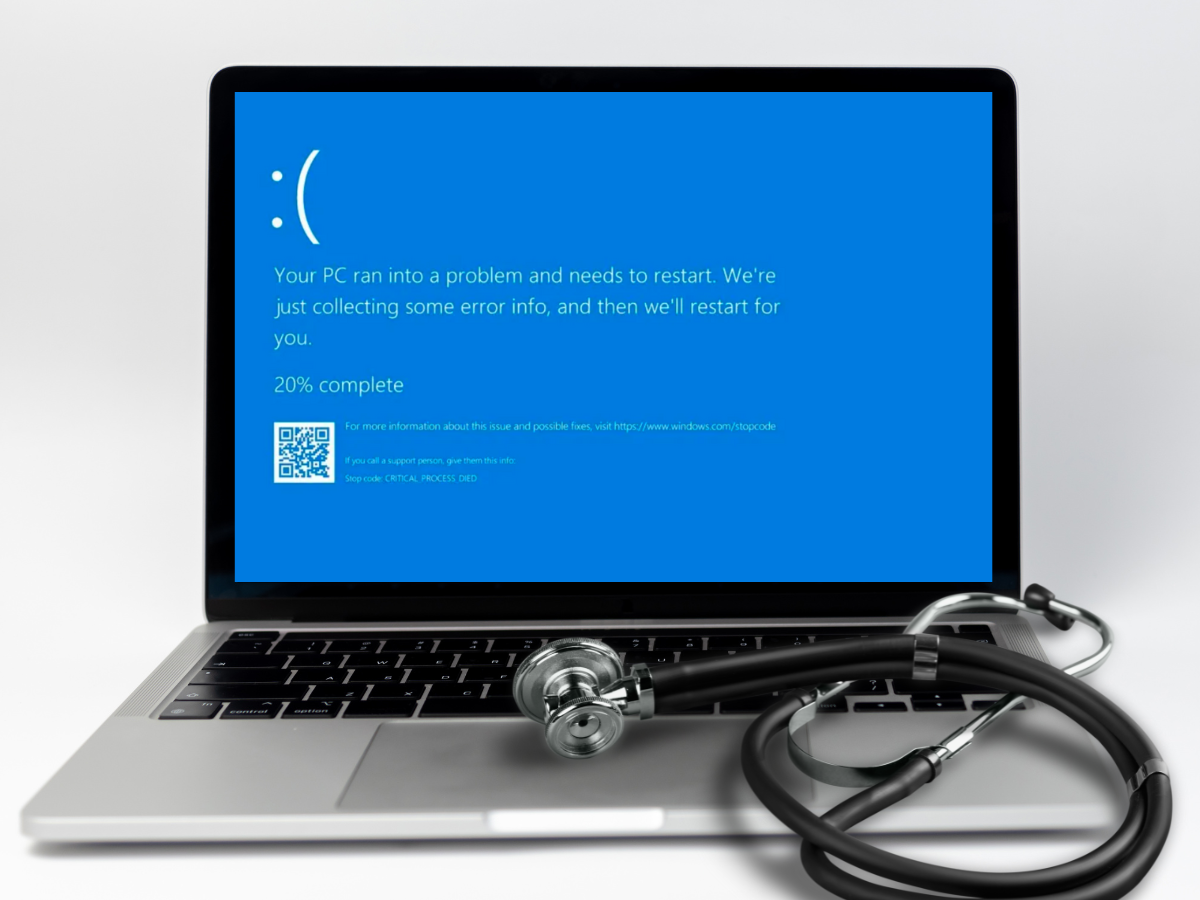
Imagine the sudden chaos when 8.5 million Windows devices - spanning industries like airlines, banking, and healthcare - began displaying the dreaded...

2 min read
In today's digital landscape, many businesses operate under the assumption that their IT networks are secure because everything seems to be running...
2 min read
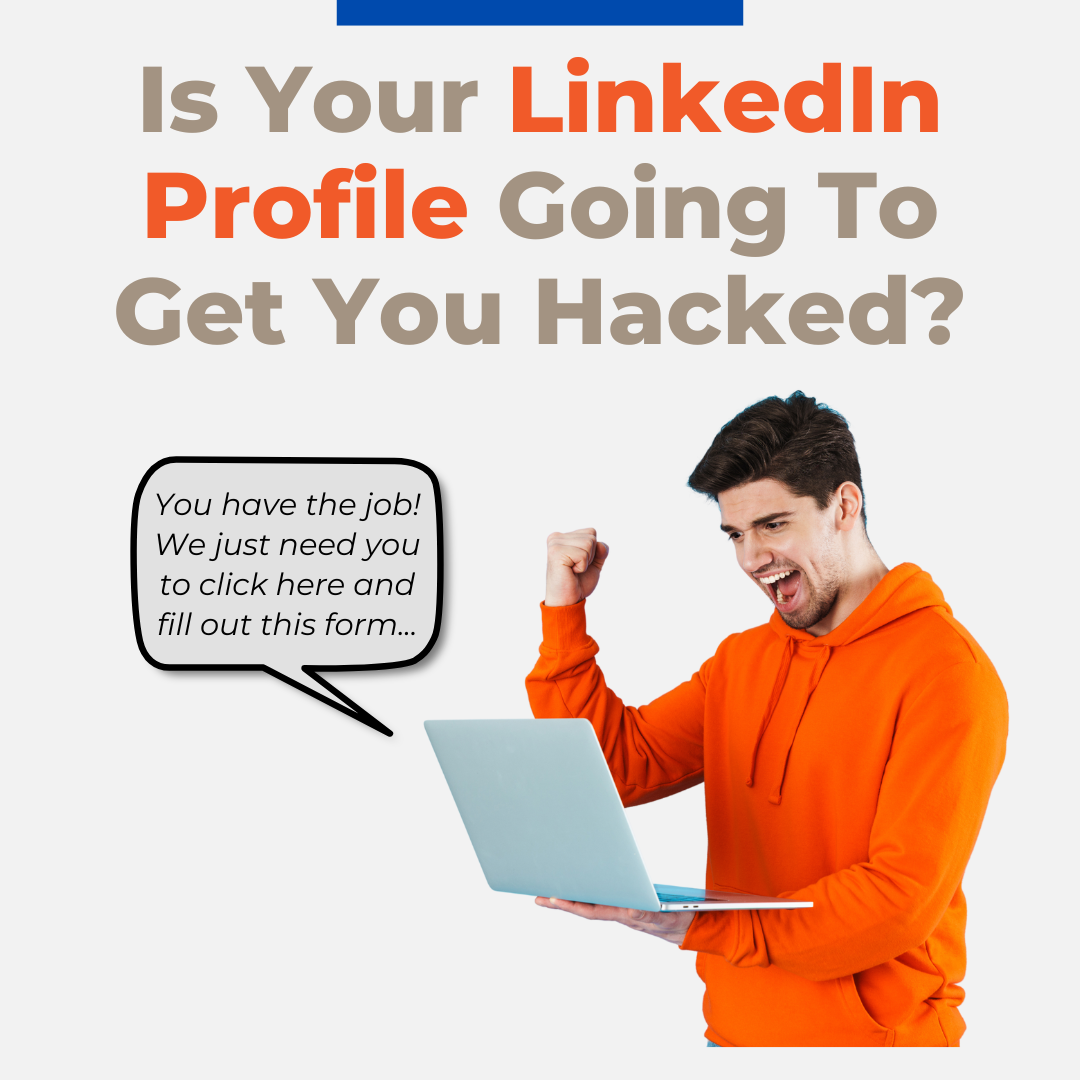
According to a recent report by Check Point Research, LinkedIn, the business platform owned by Microsoft, is impersonated in almost half of all...
.png?width=1200&height=900&name=WBA%20Issues%20%26%20Answers%20(6).png)
3 min read
A WBA Issues and Answers publication. Dan Morgan addresses regulated domains such as .bank and cybersecurity considerations around domain spoofing...

2 min read
In recent months, a significant cybersecurity breach at Change Healthcare, a payment-processing company under UnitedHealth Group, has highlighted a...

2 min read
Summer is a prime time for business owners and employees to take a much-needed vacation. Despite activating the “out of office” email responder, many...

2 min read
In early April, Omni Hotels & Resorts fell victim to a severe cyber-attack that crippled its entire IT system, leading to a company-wide outage. The...

3 min read
This true story serves as a stark warning about the devastating impact of CEO Fraud on businesses, large and small. It's essential reading for anyone...

2 min read
In the rapidly evolving digital landscape, the saying "That won't happen to me" is becoming a dangerous mindset for business owners when it comes to...

3 min read
The year 2023 marked a significant turning point for cyber-attacks with the introduction of AI (artificial intelligence), now in the hands of people...

3 min read
If you’re hoping to cut costs and boost profitability without compromising productivity or efficiency, assessing the technology you use in day-to-day...

4 min read
Tax season is around the corner, which means so are tax scams. Without fail, every year, individuals and business owners alike fall victim to tax...

3 min read
ConnectWise is addressing a critical vulnerability discovered in ConnectWise ScreenConnect, its remote desktop and access software that enables MSP...

3 min read
Long gone are the days when phones were simple devices used to make calls. Today our phones are advanced, handheld supercomputers that can do...

2 min read
Zero Trust is a relatively new cybersecurity strategy that is rapidly becoming the security model of choice for businesses. In fact, we anticipate...

3 min read
Wintertime can feel like a wonderland. There’s hot cocoa, cozy fireside conversations, glistening white snowfall…ice storms, power outages, and tons...

3 min read
Each year on February 1st, we celebrate Change Your Password Day. While it’s not a holiday that gets you off work, it serves as a good opportunity...

2 min read
In today’s hyperconnected world, cybersecurity is a critical concern for individuals and organizations alike. However, as the digital landscape...

3 min read
The infamous Xenomorph Android malware, known for targeting 56 European banks in 2022, is back and in full force targeting US banks, financial...

3 min read
Is your business plan for 2024 finalized yet? The last few months of the year can get hectic, between trying to close out the end of the quarter...

3 min read
Recently, the CEO of a very successful marketing firm had their Facebook account hacked. In just a weekend, the hackers were able to run over...

2 min read
On November 30th, Apple released an urgent update, iOS 17.1.2, that aims to patch two possible security exploits documented in 17.1.1.

3 min read
When you run your own business, it feels like there are never enough hours in the day. Even when you start early and end late, there’s always...

3 min read
With Black Friday and Cyber Monday right around the corner, here are some tips for a safe and secure online shopping experience.

3 min read
“Thank goodness” is probably what Illinois-based manufacturing company ICS thought about having a cyber insurance policy with Travelers Insurance...

3 min read
If you ask a security professional, you get by-the-book advice about sharing passwords: “Don’t share passwords.” But we know, in reality, that...

3 min read
It’s 10:00 p.m. – do you know where your children are? Google probably does. Thanks to Google Maps’ Timeline feature, the tech company probably knows...

2 min read
36% of survey participants reported installing the latest updates and software as soon as they become available. Of those who reported installing the...

2 min read
72% of respondents reported that they checked to see whether messages were legitimate (i.e. phishing or a scam) compared to 15% who reported not...

2 min read
In a recent National Cybersecurity Alliance survey, 57% of respondents said they have heard of multifactor authentication (MFA), but many people...

2 min read
Cybersecurity Awareness Month is observed every October to raise awareness about the importance of cybersecurity and promote good cybersecurity...

2 min read
October isn't just about falling leaves and pumpkin spice; it's also Cybersecurity Awareness Month, established in 2004 and dedicated to raising...

3 min read
If you’ve turned on the news sometime during the past few years, you’ve probably heard of more than one instance where a business closed due to a...