Hybrid Identity Purgatory: A Hybrid-to-Cloud Microsoft 365 Migration Story (Without Data Loss)
How a 100+ user professional services organization finished its Microsoft 365 migration — without deleting a single user account.

The cyber insurance market is getting stricter and for many organizations, it’s getting more challenging and expensive to secure coverage.
2 – 5 years ago, any industry could get cyber coverage with minimal questions asked on the cyber insurance application. But over the last 12-18 months Ransomware has become so rampant that insurance carriers really started losing a lot of money. The amount of money brought in for premiums was spent and then some on claims paid out. As a result, the applications we’re seeing today are 5+ pages of critical cybersecurity defense questions that may have you questioning the strength of your security.
According to S&P Global, June 1, 2021, The cost of standalone policies in the US climbed 28.6% in 2020
Right now, for insurance carriers, it’s a seller’s market. If they don’t get the answers to the questions on the application they’re looking for, or they’re concerned about the business or industry then they won’t approve coverage, or they’ll offer a reduced coverage amount for a higher premium.
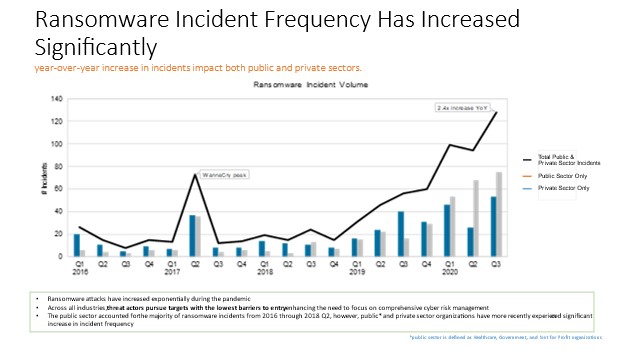
The Sophos State of Ransomware Report 2021 shows that 37% of organizations surveyed across 30 countries reported that they had experienced a ransomware attack in the past 12 months.
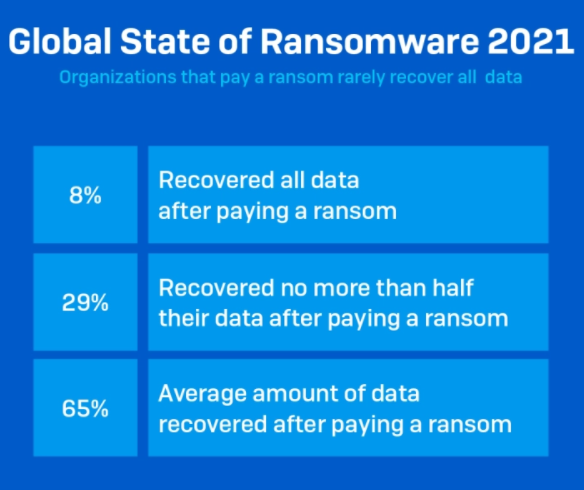
The costs involved with a ransomware attack are growing each year. The Sophos report estimates the average bill for recovering from a ransomware attack in 2021, considering downtime, people time, device cost, network cost, lost opportunity, ransom paid, etc. was $1.85 million. From that figure, the average ransomware payment to cyber criminals was only $170,404.
According to the Cybersecurity and Infrastructure Security Agency (CISA), “Cybersecurity insurance is designed to mitigate losses from a variety of cyber incidents, including data breaches, business interruption, and network damage. A robust cybersecurity insurance market could help reduce the number of successful cyber-attacks by promoting the adoption of preventative measures in return for more coverage, and encouraging the implementation of best practices by basing premiums on an insured’s level of self-protection.”
Many companies opt to go without a cyber insurance policy, with rationales ranging from the high cost of premiums to confusion about what is covered, and uncertainty about whether or not their business will suffer from a cyber incident.
Having strong cybersecurity defenses in place is a must. Let’s break down some of the questions/language present in cybersecurity applications.
1. Multi-factor Authentication
Does your business implement Multi-factor Authentication for all remote access? This includes Microsoft 365 / Google Workspace, cloud data platforms, or physical/cloud servers.
MFA has become a top prerequisite for cyber insurance coverage.
Using multi-factor authentication (MFA) is one of the easiest and most successful ways to increase the security of your organization. This can prevent hackers from taking over if they have your password.
2. Incident Response Plan
Does your organization have a formal incident response plan? How are you documenting your tabletops (testing of your IR Plan)?
Incident Response (IR) is the managed approach an organization uses to prepare, detect, contain, and recover from a cyberattack. A cyberattack or data breach can be so damaging, potentially affecting customers, intellectual property, personally identifiable information (PPI), revenue, and ultimately reputation.
Having an incident response plan in place aims to reduce this damage and recover as quickly as possible. Responding quickly and appropriately to a cyberattack can significantly reduce the impact and cost of the incident.
AND, are you testing your IR Plan with a cybersecurity tabletop exercise?
Cybersecurity tabletop exercises help organizations to identify vulnerabilities, improve incident response readiness, enhance communication and coordination, and provide a cost-effective solution to compliance and building confidence.
3. Advanced Protection Solutions
Does your business utilize an endpoint detection and response solution?
Advanced protection is increasingly a requirement in order to get cybersecurity coverage, with managed detection and response (MDR) services, and endpoint security or advanced endpoint detection and response technologies as the most common requirements.
Advanced Endpoint Protection includes next-generation protection features like advanced persistent threat detection, investigation and response, device management, data leak prevention, and others, protecting systems from file, fileless, script-based, and zero-day threats by using machine-learning or behavioral analysis.
4. Security Awareness Training
Have you implemented an employee awareness training program within your IT infrastructure?
92% of all breaches could have been prevented with a Security Awareness Training program. Security Awareness Training is a means to educate and train employees within your organization with information necessary to protect themselves as well as your organization from cybercriminals through phishing attacks, account takeovers, wire transfers, and more.
If you experience a cyber-attack and your insurer believes that you are “at fault” through weak security, they may have reason to not pay the claim. Good cybersecurity practices and solutions minimize your risk of being impacted by a cyberattack and help keep premiums and renewal costs down.
![]() Teknologize is a SOC 2 Type II accredited Managed IT and Cybersecurity provider serving small to mid-sized businesses across Washington and Oregon. We deliver full-service Managed IT Support, Co-Managed IT Support, advanced Cybersecurity Solutions, and IT Compliance Services for regulated industries, including Healthcare, Financial Institutions, the Utilities Sector, Manufacturing, and Professional Services.
Teknologize is a SOC 2 Type II accredited Managed IT and Cybersecurity provider serving small to mid-sized businesses across Washington and Oregon. We deliver full-service Managed IT Support, Co-Managed IT Support, advanced Cybersecurity Solutions, and IT Compliance Services for regulated industries, including Healthcare, Financial Institutions, the Utilities Sector, Manufacturing, and Professional Services.
👉 Book a Discovery Call to see how Teknologize can support your business.
Our Offices
Tri-Cities, Washington – 509.396.6640 | Yakima, Washington – 509.396.6640
Bend, Oregon – 541.848.6072 | Seattle, Washington – 206.743.0981
Questions about your IT or Cybersecurity? Give us a call today!
.png)
How a 100+ user professional services organization finished its Microsoft 365 migration — without deleting a single user account.
If your team uses Microsoft 365, there is a phishing attack making the rounds right now that most teams aren’t prepared to recognize yet. It does not...

It's Monday morning. You walk into the office with a plan. This is the week things move forward.